Comparexpert
Comparison Between Company

Perimeter 81 Review: What Makes Perimeter 81 Unique?
Explore this detailed Perimeter 81 review to discover what makes Perimeter 81 unique in the crowded cybersecurity market. Learn about its Zero Trust architecture, cloud-based security features, pricing, pros and cons, and why it stands out as a modern secure access solution for businesses.
Table of Contents
What Is Perimeter 81?
A Quick Look at Its Core Purpose
Perimeter 81 is a cloud-delivered SASE (Secure Access Service Edge) platform built to secure remote access, cloud resources, branch offices, and distributed teams without forcing businesses to rely on old-school hardware firewalls and clunky VPN appliances. In simple terms, it takes the mess of traditional network security and turns it into something cleaner, lighter, and much easier to manage. Instead of stacking separate tools for VPN, web filtering, firewall control, and access policies, Perimeter 81 wraps them into one centralized platform. That single-pane-of-glass approach is a huge part of its appeal, especially for IT teams that are already stretched thin.
What makes this platform relevant today is the way work has changed. Most companies no longer run from one office, one server room, and one secure network closet. Teams are remote, apps are in the cloud, contractors need temporary access, and employees switch between home Wi-Fi, coworking spaces, and mobile devices. Perimeter 81 was designed for exactly that kind of environment. It gives businesses secure access without forcing users to “dial into the office” like it’s still 2012. That’s the difference. It is not just a business VPN. It is a full access control and network security layer designed for modern work.
From Startup to Check Point SASE
Perimeter 81 started in 2018 as a fast-growing cybersecurity startup focused on replacing legacy VPNs with a more flexible, cloud-native alternative. That timing was perfect. Businesses were already shifting workloads to the cloud, and the remote work explosion only accelerated demand for tools that could secure access without slowing people down. The company gained traction quickly by offering something many traditional vendors didn’t: modern deployment, clean UX, and strong zero-trust access controls without enterprise-level deployment pain.
In 2023, Check Point Software Technologies acquired Perimeter 81 for roughly $490 million, folding it into its broader Harmony SASE / Check Point SASE portfolio. That move changed the conversation around Perimeter 81. It was no longer just a startup challenger. It became part of one of the biggest enterprise security ecosystems in the world. That matters because buyers now get the original Perimeter 81 cloud-native simplicity with the added weight of Check Point’s threat intelligence, enterprise security stack, and long-standing reputation in cybersecurity. In practice, this gives Perimeter 81 stronger enterprise credibility than many newer SASE rivals, while still keeping the product more approachable than traditional enterprise security platforms.
Why Perimeter 81 Stands Out in the SASE Market
Built for Modern Hybrid Work
A lot of security tools claim to support hybrid work. Perimeter 81 was actually built around it. That distinction matters more than most vendors admit. Many legacy vendors simply took old VPN infrastructure, moved the management panel into the cloud, and called it modern. That is like putting a fresh coat of paint on a brick wall and calling it a smart home. Perimeter 81 approached the problem differently by assuming users, apps, and devices would be everywhere from day one.
That design philosophy shows up in the way the platform handles secure access. Users can connect from laptops, mobile devices, or unmanaged contractor systems. Admins can control who gets access, what device they can use, what apps they can touch, and under what conditions they can connect. Instead of trusting everyone once they log in, Perimeter 81 keeps checking context. That is the real shift. It treats access like a guarded building with smart locks on every door, not a single front gate with one sleepy security guard. For companies with remote teams, distributed offices, freelancers, and SaaS-heavy workflows, that model is significantly more practical than legacy VPN architecture.
Zero Trust at the Center
The phrase Zero Trust gets thrown around so much it has started to sound like background noise, but in Perimeter 81’s case, it is actually central to how the platform works. The core idea is simple: trust nothing by default, verify everything continuously. Instead of assuming a logged-in user is safe, Perimeter 81 checks identity, device posture, location, and access policy before granting access to resources. That means users do not get broad network access just because they passed one login screen.
This is one of the biggest reasons Perimeter 81 feels different from traditional business VPNs. A legacy VPN often opens the front gate and gives users broad internal access once they authenticate. Perimeter 81 works more like airport security with multiple checkpoints. Even after identity is confirmed, users still need the right device, the right permissions, and the right policy context to reach sensitive resources. That layered model dramatically reduces the blast radius of compromised credentials, insider misuse, and lateral movement. In a world where stolen logins are one of the most common attack paths, that is not a luxury feature. It is table stakes.
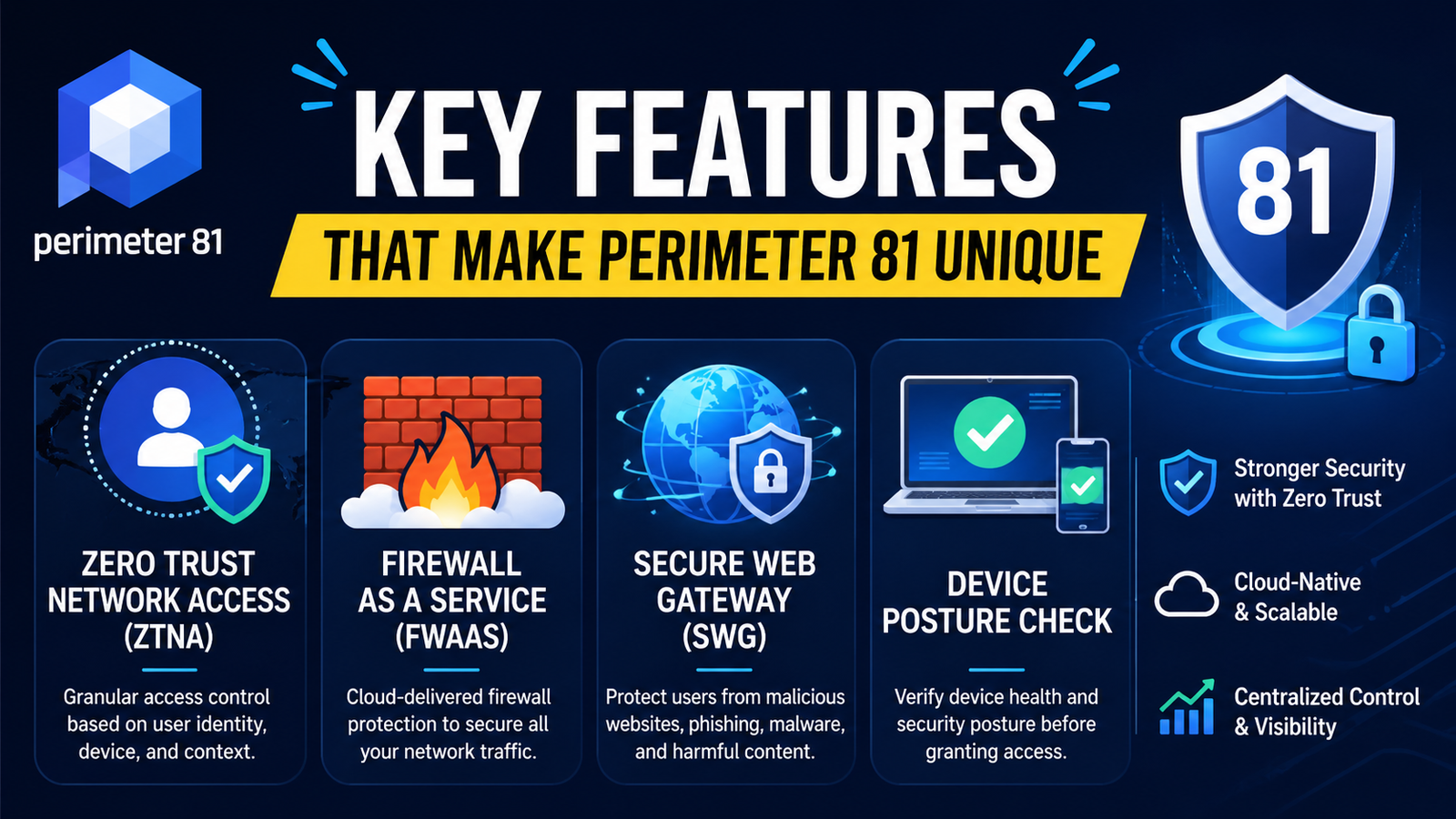
Key Features That Make Perimeter 81 Unique
Zero Trust Network Access (ZTNA)
The standout feature in Perimeter 81 is its ZTNA engine. This is the backbone of the platform and the main reason businesses choose it over a standard VPN. Instead of giving employees broad access to an internal network, ZTNA limits them to only the apps and systems they actually need. That “least privilege” model is cleaner, safer, and easier to audit.
This matters because traditional VPNs create too much trust too quickly. If one set of credentials gets compromised, attackers can often move laterally across systems. ZTNA closes that gap by shrinking access down to the application level. It is like giving someone a key to one office drawer instead of handing them the master key to the entire building. That is a huge security improvement for teams handling sensitive apps, cloud workloads, and internal systems.
Firewall as a Service (FWaaS)
Firewall as a Service is another reason Perimeter 81 stands out. Traditional firewalls are expensive, hardware-heavy, and painful to scale. Perimeter 81 shifts that control into the cloud, allowing admins to apply firewall rules across users, branches, and remote devices from one dashboard.
That means IT teams can enforce traffic rules without shipping appliances to every office or manually managing scattered edge devices. It is easier to scale, easier to update, and much easier to standardize. For growing companies, this removes a huge amount of infrastructure friction.
Secure Web Gateway (SWG)
The Secure Web Gateway feature filters web traffic and blocks risky destinations before users can interact with them. This helps stop phishing, malicious downloads, unsafe scripts, and policy violations before they become incidents.
Think of it as a security checkpoint between your users and the public internet. It keeps employees productive while quietly filtering out dangerous traffic in the background. That is especially valuable for distributed teams using unmanaged networks outside the office.
Device Posture Check
Device Posture Check adds another layer of access control by validating the health of a device before it connects. Admins can enforce rules around antivirus status, disk encryption, certificates, registry settings, and other endpoint conditions.
This is where Perimeter 81 gets much smarter than a basic VPN. It does not just ask who the user is. It also asks whether their device is safe enough to trust. That extra checkpoint reduces the risk of compromised endpoints becoming security gaps.
Always-On VPN
The Always-On VPN feature ensures users stay protected without relying on human memory. Once enabled, traffic remains secured automatically, reducing the chance that employees accidentally expose business traffic on unsafe networks.
That sounds small, but it solves a very human problem. People forget things. Security tools that depend on perfect user behavior usually fail. Always-On VPN closes that gap by making protection automatic.
Perimeter 81 Pricing and Plans
Entry-Level Costs
Perimeter 81 starts around $10 per user per month on entry plans, but pricing is not as simple as the sticker suggests. Businesses also need at least one gateway, which adds roughly $50 per month on top of user licensing. That means real monthly costs rise quickly, especially for smaller teams.
Plan | Starting Price | Key Limitation |
Essentials | $10/user/month | Gateway fee required |
Premium | $15/user/month | Higher feature access |
Enterprise | Custom | Sales-led pricing |
This pricing model is not outrageous, but it does make Perimeter 81 more expensive than many SMBs initially expect.
Is It Expensive for SMBs?
Yes, for smaller teams, Perimeter 81 can feel expensive. The per-user fee is manageable, but gateway costs and premium-tier upgrades increase total spend fast. For lean startups, that can sting.
That said, cost depends on what you compare it to. Against a consumer VPN, it looks pricey. Against buying separate tools for ZTNA, FWaaS, secure web filtering, and centralized access control, it starts to look much more reasonable. This is where Perimeter 81 wins its pricing argument. It is expensive as a VPN, but competitive as a consolidated security stack.
Ease of Use and Deployment
Setup Experience
Perimeter 81 is easier to deploy than legacy enterprise security tools, but it is not frictionless. Setup is far smoother than traditional firewall-and-VPN stacks, though first-time admins will still need some onboarding time.
The good news is that deployment is still relatively fast by enterprise standards. Reviews consistently point to quick rollout, centralized provisioning, and strong documentation. Small IT teams can usually get it running without a massive professional services engagement.
Admin Dashboard and Policy Controls
The admin dashboard is one of Perimeter 81’s strongest selling points. It is clean, centralized, and much easier to navigate than many enterprise security consoles.
Admins can manage users, gateways, policies, access rules, and device controls from one interface. That simplicity is a major differentiator. Security tools often become harder to use as they become more powerful. Perimeter 81 does a better job than most at balancing both.
Perimeter 81 vs Traditional VPN: Why the Difference Matters
One of the biggest reasons businesses look at Perimeter 81 is because traditional VPNs simply are not built for the way companies work today. A legacy VPN was designed for a time when most employees worked inside one office, connected to one central server, and used company-managed devices. That model no longer reflects reality. Modern teams work from home, coffee shops, airports, coworking spaces, and mobile devices. In that kind of environment, a traditional VPN starts to feel like using an old padlock to protect a smart building.
This is where Perimeter 81 separates itself. Traditional VPNs usually create one encrypted tunnel and then trust the user once they are inside. That means if credentials are stolen, attackers often gain broad access to internal systems. Perimeter 81 works differently because it follows a Zero Trust model. Instead of trusting users after one login, it verifies identity, device health, and access permissions every step of the way. That reduces risk significantly and gives IT teams much tighter control over who can access what.
How Perimeter 81 Improves Remote Team Security
Remote work has made business operations more flexible, but it has also created more security gaps. Employees now access company data from personal Wi-Fi, public hotspots, and unmanaged devices. That opens the door to phishing, unsafe browsing, and unauthorized access. This is exactly the type of risk Perimeter 81 was designed to solve.
With Perimeter 81, remote employees connect through a secure cloud-based network instead of relying on risky open internet connections. Every connection is encrypted, access is controlled through policy-based rules, and suspicious activity can be blocked before it becomes a serious problem. This gives businesses stronger protection without making remote work more complicated for employees.
The biggest advantage here is visibility. IT teams can see who is connecting, what device they are using, where they are connecting from, and what resources they are trying to access. That kind of centralized oversight is critical for modern remote work security. Instead of blindly trusting every login, Perimeter 81 gives businesses a way to secure distributed teams with much more precision.
Perimeter 81 for Small Businesses and Startups
Many people assume Perimeter 81 is built only for large enterprises, but that is not entirely true. While it has enterprise-grade security capabilities, the platform also works well for small businesses and startups that need stronger protection than a basic VPN can offer. This is especially true for companies with remote employees, freelancers, SaaS-heavy workflows, or sensitive customer data.
For startups, one of the biggest challenges is building secure infrastructure without creating too much operational overhead. Hiring a large IT team is expensive, and managing separate tools for VPN, firewall, web filtering, and access control can quickly become a mess. Perimeter 81 simplifies that by combining these tools into one platform. That means startups can build a more secure environment without adding unnecessary complexity.
The tradeoff is pricing. Very small businesses may find it more expensive than basic alternatives. Still, for startups that need secure remote access, centralized control, and scalable cloud security, Perimeter 81 can be a strong long-term investment rather than just another monthly software expense.
Perimeter 81 Pros and Cons
Pros
- Excellent Zero Trust architecture
- Strong cloud-native deployment
- Clean admin dashboard
- Strong remote workforce support
- Consolidates multiple security tools
Cons
- Pricing rises fast
- Gateway fees add complexity
- Some policy setup has a learning curve
- Best support reserved for higher tiers
- Can be overkill for very small teams
Security Performance and Compliance
Encryption Standards
Perimeter 81 supports strong encryption and secure protocols including WireGuard, OpenVPN, and IKEv2, along with enterprise-grade encryption standards designed for secure business traffic. That gives organizations flexibility without sacrificing baseline security.
Compliance and Audit Readiness
Perimeter 81 supports compliance frameworks like SOC 2, ISO 27001, HIPAA, and GDPR, making it a practical fit for regulated industries. That matters for companies that need access controls and audit trails, not just secure tunnels.
Perimeter 81 User Experience and Dashboard Simplicity
One area where Perimeter 81 consistently earns praise is usability. Security software often feels overwhelming, especially for small IT teams that do not have time to navigate complex enterprise dashboards. Many cybersecurity tools are powerful, but they are also cluttered, confusing, and difficult to manage. Perimeter 81 takes a different approach.
Its dashboard is clean, modern, and designed with usability in mind. Admins can manage users, policies, gateways, access controls, and network settings from one central interface. That simplicity is one of the platform’s biggest strengths because it reduces operational friction. Security becomes much easier to manage when the tools are organized and accessible instead of buried under layers of menus and outdated design.
Also Read
Lasting Dynamics Review: Is Lasting Dynamics a Reliable Tech Partner?
Woolx Review: Comfort, Quality & Pricing
Credit Glory Review: Does It Really Improve Your Score?
Virtual Sheet Music, Inc. Review: Best Platform for Musicians?
How Uniplaces Works for Booking Student Accommodation
Is Perimeter 81 Worth It in 2026?
The real question for many buyers is simple: is Perimeter 81 actually worth paying for in 2026? The answer depends on what a business needs. If the goal is just basic encrypted browsing, then Perimeter 81 may feel too advanced and too expensive. There are cheaper tools for simple VPN access.
But if a business needs more than a VPN, the value becomes much clearer. Perimeter 81 is not just selling encrypted tunnels. It offers a full cloud-delivered security layer with Zero Trust Network Access, secure web filtering, device posture checks, centralized policy control, and scalable network security. Buying those tools separately usually costs more, takes longer to deploy, and creates more operational complexity.
Who Should Use Perimeter 81?
Perimeter 81 is best for SMBs, mid-market companies, distributed teams, and security-conscious organizations that need more than a simple VPN. It is especially strong for companies juggling remote employees, contractors, SaaS sprawl, and cloud infrastructure.
It is less ideal for tiny teams that only need basic encrypted browsing. If all you need is a simple tunnel, this is probably too much platform. If you need centralized access control, audit-ready policies, and cloud-native zero trust security, Perimeter 81 becomes much more compelling.
Conclusion
Perimeter 81 stands out because it is not trying to be just another business VPN. Its real value comes from turning remote access into a broader Zero Trust security layer that is easier to deploy than legacy enterprise tools and far more capable than standard VPN software. That is what makes it unique. It combines ZTNA, FWaaS, SWG, device posture checks, and centralized policy management into one platform that actually feels designed for modern work.
It is not the cheapest option on the market, and smaller businesses may hesitate at the pricing structure. Still, for organizations that need secure remote access without stitching together five separate tools, Perimeter 81 makes a strong case for itself. It is best understood not as a VPN replacement, but as a smarter access and security platform built for the way businesses operate now.
Frequently Asked Questions
No. Perimeter 81 includes VPN functionality, but it is much broader than a business VPN. It combines secure access with zero trust controls, firewall services, web filtering, and policy-based access management.
Yes, but mostly for small businesses with real security needs. It can be expensive for tiny teams, though it delivers strong value for SMBs managing remote access and cloud resources.
The biggest difference is Zero Trust. Traditional VPNs trust users too quickly. Perimeter 81 verifies users, devices, and policies continuously before granting access.
Yes. Check Point acquired Perimeter 81 in 2023 and integrated it into its broader Check Point SASE / Harmony SASEportfolio.
For companies that need modern secure access, centralized controls, and stronger security than a standard VPN can offer, yes. For very small teams needing only basic encrypted access, it may be more than necessary.
Table of Contents
Related Post


Lasting Dynamics Review: Is Lasting Dynamics a Reliable Tech Partner?
Nihaojewelry Review 2026: Is Nihaojewelry Worth It for Wholesale Jewelry?